Recent industry reports show that the average DDoS attack size has surpassed 1 Tbps, with some exceeding even more. Global DDoS attacks increased by over 50% year-over-year, driven by the availability of cheap botnet access on the dark web. Over 40% of organizations experience repeated DDoS attacks, often used as a distraction for more serious intrusions like data theft or ransomware. As businesses become increasingly digital, understanding DDoS attacks is essential for securing networks, applications, and customer trust.
Key DDoS Statistics
- The most significant recorded DDoS attack exceeded several terabits per second (Tbps).
- Some botnets include hundreds of thousands of compromised devices.
- Application-layer (Layer 7) DDoS attacks have increased by over 70%, targeting APIs and web services.
- The average DDoS attack lasts between minutes and several hours, but some campaigns can extend for days or weeks.
- The global cost of DDoS disruptions is estimated in the billions of dollars annually.
What Is a DDoS Attack?
A Distributed Denial of Service (DDoS) attack is a cyberattack that aims to overwhelm a server, network, or service with excessive traffic from multiple compromised devices, typically forming a botnet. The objective is simple: make the targeted service unavailable to legitimate users.
Unlike a regular DoS attack, which originates from a single source, DDoS attacks leverage distributed systems, making them significantly more powerful and more challenging to mitigate.
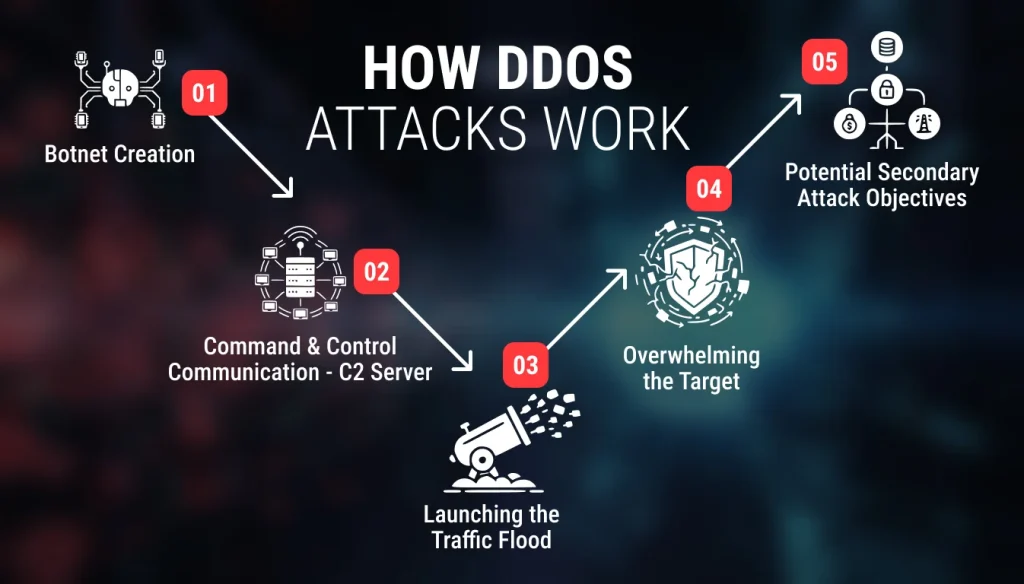
How DDoS Attacks Work?
To understand how DDoS attacks work, it helps to break the process into key stages:
1. Botnet Creation
Hackers first build a botnet, which is a network of compromised devices infected with malware. These devices can include:
- Computers
- Servers
- IoT devices (CCTV cameras, routers, smart home devices)
- Mobile phones
2. Command and Control Communication (C2 Server)
The attacker uses a Command and Control (C2) server to communicate with the botnet.
The attacker can:
- Activate the botnet
- Send attack instructions
- Update malware
- Coordinate timing and traffic patterns.
3. Launching the Traffic Flood
Once commanded, the botnet simultaneously sends a massive volume of traffic to the target. The type of traffic depends on the attack category:
Volume-based attacks
Flood the target with high traffic (e.g., UDP floods).
Protocol-based attacks
Exploit weaknesses in server protocols (e.g., SYN floods).
Application-layer attacks
Overwhelm the application with legitimate-looking requests (e.g., HTTP floods).
Regardless of the type, the intent is the same:
Exhaust the target’s resources
- CPU
- Memory
- Bandwidth
- Network sockets
- Application thread capacity
4. Overwhelming the Target
As the target’s resources reach their limits, the system can:
- Slow down
- Reject legitimate users
- Crash or reboot
- Become completely inaccessible
In large-scale attacks, this outage can extend across different systems, including:
- Website front ends
- APIs
- Databases
- DNS services
- Cloud infrastructure
5. Potential Secondary Attack Objectives
While many DDoS attacks aim purely to cause disruption, others serve as a distraction for:
- Data theft
- Ransomware deployment
- Financial fraud
- Network infiltration
Common Types of DDoS Attacks
DDoS attacks vary based on the network layer they target or the method used. The major types include:
1. Volume-Based Attacks (Layer 3/4)
These attacks aim to saturate the target’s bandwidth with massive amounts of traffic. The goal is to consume all available network capacity, preventing legitimate users from accessing it.
Common Volume-Based Attacks:
• UDP Flood
Sends large numbers of UDP packets to random ports, causing the server to check for listening applications and respond with ICMP packets repeatedly.
• ICMP Flood (Ping Flood)
Overwhelms the server with continuous ICMP Echo Request packets, resulting in high CPU and bandwidth consumption.
• DNS Amplification
Abuses open DNS resolvers to send amplified responses to the target, generating traffic far larger than the attacker sends.
• NTP Amplification
Uses vulnerable NTP servers to multiply the size of traffic delivered to the victim.
2. Protocol-Based Attacks (Network Layer Attacks)
Protocol attacks exploit vulnerabilities in network protocols or connection-handling mechanisms. They aim to exhaust server resources, such as connection tables or processing power.
Common Protocol-Based Attacks:
• SYN Flood
Sends a large number of SYN packets to initiate TCP connections but never completes the handshake, filling the server’s connection table.
• Ping of Death
Sends malformed or oversized packets that cause system crashes or buffer overflows.
• Smurf Attack
Involves spoofing the victim’s IP and using ICMP broadcast to flood it with response packets.
• Fragmentation Attacks (Teardrop, IP Fragmentation)
Send overlapping or malformed packet fragments that the server cannot properly reassemble.
3. Application Layer (Layer 7) Attacks
These attacks target the application or web server directly, often using legitimate-looking traffic to bypass security measures. They are harder to detect because they mimic normal user behavior.
Common Layer 7 Attacks:
• HTTP GET/POST Flood
Sends large numbers of seemingly valid HTTP requests to overload the web server or application.
• Slowloris
Maintains many open connections by sending partial HTTP requests slowly, keeping server resources locked.
• API Exhaustion Attacks
Spam API endpoints with requests, causing service slowdowns or failures.
• DNS Query Flood
Targets DNS servers with continuous queries, degrading DNS performance or causing a complete outage.
DDoS Attack Examples
- Google HTTP/2 Rapid Reset Attack (October 2023)
- In 2023, Google mitigated a record-breaking DDoS attack that peaked at 398 million requests per second (RPS).
- This used a “Rapid Reset” technique in the HTTP/2 protocol, where attackers send requests and immediately cancel them, overwhelming servers by repeatedly opening and closing connections.
- This attack highlighted a severe weakness in how HTTP/2 handles stream cancellation, prompting cloud providers and web operators to enhance their mitigation strategies for this vector.
- Large-Scale Volumetric Attack Against an ISP (Late 2024)
- According to SOCRadar on October 29, 2024, Cloudflare mitigated a massive 5.6 Tbps DDoS attack targeting an unnamed Internet Service Provider (ISP) in East Asia.
- The attack was traced to a Mirai-botnet variant, leveraging more than 13,000 compromised IoT devices.
- On average, there were about 5,500 unique source IPs per second, each contributing roughly 1 Gbps of malicious traffic.
- This incident underscores the ongoing significance of IoT devices as a crucial enabler for botnets that can generate multi-Tbps traffic.
- According to SOCRadar on October 29, 2024, Cloudflare mitigated a massive 5.6 Tbps DDoS attack targeting an unnamed Internet Service Provider (ISP) in East Asia.
- Proliferation of “Gayfemboy” Malware (2024–2025)
- “Gayfemboy” is a more recent Mirai-family malware strain discovered in February 2024.
- It infects a variety of devices (like routers from TP-Link, DrayTek, Cisco) and has been used to build botnets for DDoS attacks targeting companies across multiple countries.
- The emergence of this strain highlights how botnet builders are adapting their malware to target various types of IoT hardware, thereby expanding the scale and reach of attacks.
- “Gayfemboy” is a more recent Mirai-family malware strain discovered in February 2024.
- Dark Storm Team and the X (Twitter) Outage (March 2025)
- The Dark Storm Team, a pro-Palestinian hacktivist group active since late 2023, has conducted multiple DDoS campaigns.
- On March 10, 2025, they claimed responsibility for a DDoS attack on X, causing widespread disruption.
- This example illustrates how DDoS is not just a tool for financial attackers; it is also used in politically motivated hacktivism.
- The Dark Storm Team, a pro-Palestinian hacktivist group active since late 2023, has conducted multiple DDoS campaigns.
- Record Number of DDoS Attacks in Early 2025
- Cloudflare’s Q1 2025 report shows they mitigated 20.5 million DDoS attacks in just that quarter, nearly matching the total for all of 2024.
- Among these were hyper-volumetric attacks, including a UDP flood reaching 4.8 Bpps (packets per second).
- One particularly massive attack (mid-2025) sent 37.4 terabytes of data in just 45 seconds, peaking at 7.3 terabits per second (Tbps).
- The attack leveraged multiple vectors: UDP floods, reflection techniques, and Mirai-based botnet traffic.
- Cloudflare’s Q1 2025 report shows they mitigated 20.5 million DDoS attacks in just that quarter, nearly matching the total for all of 2024.
- Infrastructure-Focused DDoS Surge (H1 2025)
- According to a Link11 Cyber Report, in the first half of 2025, DDoS attacks increased by 225% compared to the first half of 2024.
- They also documented new tactics, including massive data volumes (up to 438 TB per campaign) and an increase in Layer 7 (application-layer) attacks that mimic normal user behavior.
- These attacks frequently targeted critical infrastructure, demonstrating how attackers are combining scale and sophistication to achieve their objectives.
- According to a Link11 Cyber Report, in the first half of 2025, DDoS attacks increased by 225% compared to the first half of 2024.
- State Linked and Geopolitical Targeting (2024)
- In Arelion’s 2025 threat landscape report, it was noted that state-linked or politically motivated actors increasingly targeted subsea internet cables and critical infrastructure using DDoS attacks.
- In 2024, a massive multi-vector attack utilized TCP SYN + DNS amplification, achieving a throughput of 4.2 Tbps, and targeted Cloudflare’s infrastructure.
- Packet-rate extremes were also recorded, with bursts reaching up to 440 million packets per second (Mpps), especially via UDP floods.
- In Arelion’s 2025 threat landscape report, it was noted that state-linked or politically motivated actors increasingly targeted subsea internet cables and critical infrastructure using DDoS attacks.
What are some Prominent DDoS Attack Detection Methods?
Early detection is crucial for minimizing damage. Common methods include:
1. Traffic Anomaly Detection
Traffic anomaly detection tools continuously monitor network traffic patterns and trigger alerts when unusual behavior is detected.
Indicators of anomalies include:
- Sudden spikes in inbound traffic
- Unusual traffic sources or geolocations
- Abnormally high packets per second (PPS) or requests per second (RPS)
- Increased connection attempts from the same IP range
2. Signature-Based Detection
Signature-based systems compare incoming traffic to known patterns of malicious behavior.
Effective for detecting:
- Known DDoS botnets
- Recognizable attack payloads
- Familiar vectors like SYN flood, UDP flood, or Smurf attacks
3. Behavioral Analytics
Behavior-based detection focuses on how users and traffic behave over time rather than relying on fixed signatures.
Behavior analysis detects:
- Abnormal request repetition
- Bots mimicking legitimate user behavior.
- Layer 7 anomalies, such as excessive API calls
- Slow or partial HTTP requests (e.g., Slowloris)
This method is crucial for detecting application-layer DDoS attacks, which are often subtle and designed to evade traditional filters.
4. Rate-Based Detection
Systems monitor the speed at which requests or packets are sent to a service.
Triggers may include:
- Too many requests per second from a single IP
- High volumes of SYN packets
- Excessive failed connection attempts
- Rapid-fire API calls
5. Deep Packet Inspection (DPI)
DPI examines packet headers and payloads to evaluate whether traffic is legitimate. DPI is beneficial for detecting protocol attacks, such as TCP SYN floods or fragmented packet attacks.
DPI helps detect:
- Malicious packet structures
- Spoofed source IPs
- Protocol anomalies
- Packets crafted to exhaust resources
6. NetFlow and Log Analysis
NetFlow (or similar flow analysis tools, such as sFlow) provides insights into traffic patterns, allowing security teams to identify suspicious flows. Automated log correlation in SIEM platforms can also detect early indicators of DDoS activity.
Useful for detecting:
- Large-scale outbound or inbound traffic surges
- Traffic from an unusual geographic distribution
- Long-lasting, low-rate attacks
- Multi-vector attack patterns
7. DNS Traffic Monitoring
DNS is a frequent target for DDoS attacks. Monitoring DNS traffic can reveal Layer 7 and reflection-based attacks.
Monitoring looks for:
- Excessive DNS queries
- High NXDOMAIN response rates
- Repeated requests from the same IP or botnet
- Sudden spikes in amplification responses
8. Real-Time Alerts from IDS/IPS
Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) detect attack patterns and anomalies.
IDS/IPS can detect:
- Known DDoS signatures
- Protocol violations
- Spoofed traffic
- Sudden traffic bursts
9. Global Threat Intelligence Feeds
Threat intelligence feeds provide data on emerging DDoS vectors, malicious IPs, and evolving botnet signatures.
These feeds help detect:
- Traffic from known botnet IP ranges
- Attacks that match global trends
- Repeat offenders across multiple organizations.
10. Cloud-Based DDoS Monitoring
Cloud providers such as Cloudflare, AWS Shield, and Akamai offer large-scale detection systems that leverage global traffic visibility.
These systems detect:
- Cross-network patterns
- Distributed, multi-region attacks
- Massive volumetric surges
- Emerging attack techniques (HTTP/2 Rapid Reset)
What are some Important DDoS Mitigation Strategies?
Mitigating DDoS attacks requires multi-layered security measures:
1. Content Delivery Networks (CDNs)
CDNs play a critical role in mitigating DDoS attacks by distributing content across a vast network of global servers. When a website is targeted, the incoming traffic is absorbed and spread throughout the CDN infrastructure, preventing the origin server from becoming overwhelmed. By caching content and distributing load, CDNs minimize single points of failure and ensure websites remain accessible even during high-volume DDoS events. This approach is efficient for handling Layer 7 attacks that target website interfaces and APIs.
2. Web Application Firewalls (WAFs)
A Web Application Firewall provides an essential layer of protection against application-level DDoS attacks. WAFs analyze incoming HTTP traffic and block malicious patterns such as bot-generated requests, abnormal payloads, or suspicious user behavior. They are also capable of filtering out slow and partial requests, such as those used in Slowloris attacks that attempt to exhaust server resources. By distinguishing legitimate traffic from potentially harmful traffic, WAFs help maintain application stability during high-intensity attacks.
3. Rate Limiting and Traffic Throttling
Rate limiting is a simple yet powerful way to prevent DDoS attacks from overwhelming a service. By capping the number of requests an individual IP address or user can make within a given timeframe, rate limiting minimizes the impact of automated request floods. When suspicious traffic spikes occur, dynamic throttling can be activated to tighten request limits further. This ensures APIs, login endpoints, and application servers remain responsive and secure, even during targeted abuse attempts.
4. IP Reputation Filtering and Botnet Blocking
Modern DDoS protection relies heavily on identifying and blocking known malicious IP addresses. IP reputation systems, often powered by global threat intelligence, maintain a constantly updated database of harmful IP ranges, botnets, and compromised devices. When attackers launch an attack, traffic from these known sources can be filtered out automatically before it hits the network. This approach significantly reduces the volume of malicious traffic, enabling organizations to stay ahead of attacks using widely recognized botnets.
5. Traffic Scrubbing Centers
Traffic scrubbing centers are large-scale, high-capacity facilities designed to clean incoming traffic before it reaches an organization’s network. During a DDoS attack, traffic is rerouted to the scrubbing center, where advanced filters separate legitimate packets from harmful ones. Only clean traffic is then passed back to the target environment. This technique is vital for absorbing massive volumetric attacks, often exceeding hundreds of gigabits per second, that could otherwise overwhelm even well-prepared networks.
6. Anycast Network Routing
Anycast routing enhances DDoS resilience by allowing multiple servers across different regions to share the same IP address, thereby distributing the load across multiple servers. When a DDoS attack occurs, traffic is automatically routed to the nearest or least-burdened server, distributing the load across the entire network. This prevents any single server from being overwhelmed and ensures high availability even during large-scale, globally distributed attacks. Many major cloud providers rely on Anycast to deliver unmatched resiliency and scalability.
7. Load Balancing and Redundancy
Load balancing helps distribute incoming connections across multiple servers or data centers, preventing bottlenecks and reducing the risk of system overload. When combined with redundancy, where numerous backup systems are kept active, load balancers ensure that even if one server fails due to attack traffic, others remain operational. This strategy significantly enhances service reliability during DDoS events, making it more challenging for attackers to bring the entire system offline.
8. Intrusion Detection and Prevention Systems (IDS/IPS)
IDS and IPS technologies monitor network traffic for signs of malicious behavior, suspicious patterns, or known attack signatures. When these systems detect protocols being abused or packets designed to exploit vulnerabilities, they generate alerts or automatically block the traffic. IDS/IPS solutions work particularly well against protocol-level attacks such as SYN floods, malformed packets, or connection table exhaustion, providing a crucial layer of defense for network infrastructure.
9. Overprovisioning Bandwidth
While not a standalone solution, overprovisioning bandwidth offers a temporary buffer against moderate DDoS attacks. By allocating more bandwidth than usually required, organizations can absorb short-term traffic surges before triggering mitigation mechanisms. However, since large modern DDoS attacks can exceed terabits per second, bandwidth overprovisioning should always be combined with more advanced defensive technologies.
10. Cloud-Based DDoS Protection Services
Cloud-based DDoS protection services such as Cloudflare, AWS Shield, Akamai, and Google Cloud Armor are among the most effective defenses available today. These services leverage vast global networks capable of absorbing multi-terabit attacks and detecting malicious traffic patterns instantly. With features like automated bot filtering, multi-vector attack mitigation, and adaptive learning, cloud-based protection offers unmatched scalability and reliability for businesses of all sizes.
11. DNS Hardening and Redundancy
DNS infrastructure is a frequent target of DDoS attacks, making DNS hardening an essential mitigation strategy. Techniques such as using multiple DNS providers, implementing Anycast DNS, enabling DNSSEC, and applying query rate limits help protect against both volumetric and application-level DNS attacks. By preventing DNS servers from becoming a single point of failure, organizations can maintain accessibility even during large-scale disruptions.
12. Incident Response Planning and Testing
A well-designed DDoS incident response plan enables an organization to react quickly and effectively when an attack occurs. This plan should outline escalation procedures, communication strategies, automated alert configurations, and clearly defined roles for IT and security teams. Regular drills and simulation exercises help teams stay prepared and reduce downtime during real attacks. Companies that practice incident response are far more resilient and able to contain damage swiftly.
Impact of DDoS Attacks
DDoS attacks can have severe consequences:
1. Service Disruption and Downtime
- Websites, applications, APIs, or entire networks become slow or unavailable.
- Customers may be unable to access critical services, resulting in frustration and a loss of trust.
- Industries such as banking, e-commerce, healthcare, and telecom experience immediate operational disruptions.
2. Significant Financial Losses
- Loss of revenue due to halted transactions or downtime.
- High costs for DDoS mitigation tools, emergency response, and system recovery.
- Increased bandwidth usage fees from cloud providers due to massive traffic spikes.
- Potential penalties or SLA breaches for service interruptions.
3. Increased Security Risks
- Attackers often use DDoS attacks as a distraction to conduct deeper attacks, such as data theft or ransomware.
- Overloaded security teams may miss indicators of compromise during the chaos.
- Exploited vulnerabilities can lead to long-term breaches and persistent threats.
4. Reputational Damage
- Customer trust declines when a company repeatedly experiences outages.
- Negative press coverage can harm the brand’s public image.
- Competitors may gain an advantage as customers seek more reliable alternatives.
5. Operational Disruption
- IT and security teams are often diverted from their regular tasks to focus on crisis management.
- Employees may face stress, longer hours, and burnout during prolonged periods of attack.
- Routine business processes and ongoing projects often stall or fall behind schedule.
6. Long-Term Business Impact
- Loss of customers due to poor service reliability.
- Increased spending on infrastructure upgrades and stronger cybersecurity measures.
- Potential legal or compliance consequences if critical services fail.
7. Collateral Damage Across the Ecosystem
- Attacks on ISPs, DNS providers, or cloud platforms can affect multiple businesses.
- Third-party dependencies amplify the impact beyond the original target.
- Entire regions or industries may experience temporary connectivity or service issues.
Conclusion
DDoS attacks continue to pose a significant threat to organizations worldwide, targeting a wide range of entities, from small websites to large enterprises. With attackers constantly developing new methods, businesses must adopt a proactive defense strategy built on strong detection, mitigation, and continuous monitoring.
Understanding how DDoS attacks work and preparing for them can significantly reduce downtime, financial losses, and long-term damage. As cyber threats evolve, staying informed and investing in robust security tools is essential for resilient digital operations.
FAQs
Here are some frequently asked questions (FAQs).
1. How long do DDoS attacks typically last?
They can last from a few minutes to several hours. Some sophisticated campaigns may persist for days or even weeks with intermittent attack waves.
2. Can you prevent DDoS attacks completely?
No security system can prevent DDoS attacks. Strong mitigation strategies, layered defenses, and real-time monitoring can dramatically reduce the risk and impact.
3. What is a botnet in DDoS attacks?
A botnet is a network of compromised devices controlled by an attacker. It is used to generate massive traffic during a DDoS attack.
4. What’s the difference between DoS and DDoS?
DoS (Denial of Service): An attacker or device floods the target with excessive traffic.
DDoS (Distributed Denial of Service): Multiple devices simultaneously attack the target, making it far more powerful and more challenging to stop.
Table of Contents
