Cyber Threats
 Bisma Farrukh - May 22, 2026
Bisma Farrukh - May 22, 2026What Is a Social Engineering Attack? Types, Techniques, & Prevention
Another 2025 report found that social engineering attacks accounted for 36% of all cyber intrusions, making it one of the most common attack methods used by cybercriminals today. In this blog, we will explore social engineering attacks, their examples, and ...See More
 Bisma Farrukh - Apr 13, 2026
Bisma Farrukh - Apr 13, 2026Remote Access Trojan (RAT): What It Is and How to Detect and Remove It?
Introduction Unlike typical viruses, RATs allow hackers to silently control your device from anywhere in the world. From stealing sensitive data to spying through your webcam, RAT malware poses a serious risk to both individuals and businesses. In this guide, ...See More
 Bisma Farrukh - Mar 25, 2026
Bisma Farrukh - Mar 25, 2026Telegram Scams: Common Telegram App Scams and How to Stay Safe?
One platform that has increasingly attracted scammers is Telegram. With its large user base, privacy-focused features, and minimal moderation in some areas, the platform has become a popular tool for cybercriminals. Telegram scams range from fake investment groups to cryptocurrency ...See More
 Arsalan Rathore - Mar 9, 2026
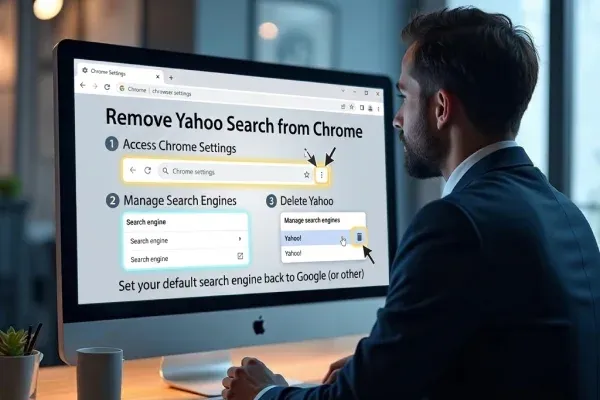
Arsalan Rathore - Mar 9, 2026How to Remove Yahoo Search from Chrome
You didn’t change anything. You didn’t ask for this. And yet, here it is, redirecting you every single time. This isn’t a glitch, and it’s not something Chrome did on its own. If Yahoo Search has quietly taken over your ...See More
 Bisma Farrukh - Dec 29, 2025
Bisma Farrukh - Dec 29, 2025What Is a Botnet? Understanding Botnet Attacks and DDOS threats
Introduction Botnets quietly infect thousands or even millions of devices, turning them into remote-controlled weapons that can launch devastating attacks. From overwhelming websites with traffic to stealing sensitive information, botnets play a central role in modern cybercrime. This blog explains ...See More
 Bisma Farrukh - Dec 2, 2025
Bisma Farrukh - Dec 2, 2025What is Clone Phishing? How It Works & How to Stay Safe
Unlike generic phishing attempts that are easy to spot, clone phishing uses legitimate messages that victims trust, making it one of the most dangerous social engineering tactics. According to cybersecurity reports, over 94% of malware is delivered via email, and ...See More